When biometric identification isn’t sufficient
Biometrics is being hailed as one of the most secure means of providing digital security. Biometrics are in use to ensure identities are protected both online or at physical locations such as airports and ATMs. Iris scanners, voice identification, fingerprint readers, and retina identification are all in use to varying extents.
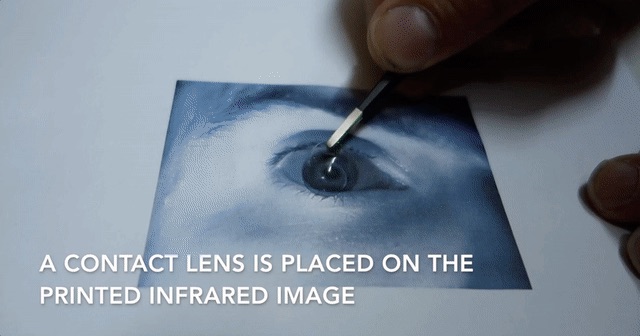
Are biometrics the panacea of identity protection? Not necessarily. Last month, a hacker named Jan Krissler showed the tech community just how easy it could be to beat biometric security. With a low-tech hack, he defeated the high-tech security biometric scanning feature on a Galaxy S8.
According to The Verge, “[Krissler was] able to take [an] infrared picture of a person’s face using the night mode setting on a regular point and shoot camera. Print it out on an ordinary laser printer and it fools the camera by placing a contact lens over the image to give it the appearance of an actual human eye.”
While the hack was relatively straightforward, biometrics are still more secure than most passwords. (Did you know that the most common LinkedIn password from the 2016 data breach was 123456?) But unlike passwords, if your biometrics are hacked, there’s no “reset” option.
To scan or not to scan? With biometrics, the answer may be to scan TWICE.
A Harvard Business Review’s article states, “Identity verification through biometrics can ensure greater security for personal information, while also providing customers with a more seamless experience in the digital environment of smartphones, tablets, sensors, and other devices.” The article goes on to say that applying multiple mechanisms at once, or biometric modalities, provide a higher level of security than a single biometric measure.
“While a bad actor could feasibly gain access to your thumbprint on the specific device it is stored on or to your digital voiceprint, if an app simultaneously requires a thumbprint, a retina scan, and a vocal recognition signature, it would be close to impossible for a bad actor to replicate that in the seconds needed to open the app,” per Harvard Business Review.
New research is now focusing on adding additional layers of security by requiring two or more types of biometrics for secure identification.
Multimodal Biometric Research
Image processing and analysis play a key role in both research papers detailed below. For these projects, MATLAB was used for image processing and analysis.
The first paper on multimodal biometric security combined simultaneous analysis of palm prints and iris pattern matching. The research was summarized in the paper An efficient technique of multimodal biometrics using fusion of face and iris features.
While fingerprint readers have been the mainstay of many commercial devices, palms may be better suited to the task of biometric identification. Your palm has creases and ridges that are formed before birth and some creases are added as we age. Even genetically identical twins have unique palmprints. The highly randomized appearance of the creases and lines make palmprints a suitable choice for biometric identification.
For palmprint recognition, the image was binarized. Then image boundaries were located before key points were identified. The principal lines in the central part of the palm were identified and the contrast of the picture was increased. This simplified the image and enabled the size of the data required to be minimized.
The team also used iris pattern matching, since iris scans are a very reliable method to accurately identifying someone. The colored pattern peoples’ eyes are extremely complex and unique. Iris pattern matching is estimated to be 10 times more accurate for identification than fingerprinting. The team’s image analysis extracted the boundaries and segmented the images for simplified processing.
The team concluded that requiring two biometric authentications increased the accuracy of a match.
The second paper combined biometric modalities with standard security measures. When using two biometric measures is not secure enough, the approach could be augmented by the use of standard password or PIN. So, even if a thief were to create a fake iris image, they would still need your password or PIN to access your device or secure account.
This is exactly the approach taken by a second group of researchers: They combined multimodal biometrics with standard PIN/QR code authentication. The paper titled Multi-level Security using QR Code, Biometrics, and Password for Security Systems was published in the International Journal of Engineering Science and Computing.
The paper detailed how combining iris recognition and fingerprint scanning with common security methods such as passwords, PINS, or QR codes resulted in increased security for customers of ATMs and other secure locations. Both the fingerprint analysis and iris recognition used in the paper relied on image processing.
As criminals and hackers find new ways to access secure logins, research will continue to find new ways to secure our data in an increasingly digital world. The level of security can be increased as needed with multimodal biometrics. For example, simply checking the balance on your bank account could use a single security measure, while making a withdrawal could require two means of biometric security.
Here are some links for more information on this topic:
- Here is the video of the Samsung iris hack.
- The Verge article, Hacker beats Galaxy S8 iris scanner using an IR image and a contact lens.
- Fortune’s article, Here Are the Most Common Passwords Found in the Hacked LinkedIn Data.
- Harvard Business Review’s article, Passwords are terrible, but Will Biometrics Be Any Better?
 Cleve’s Corner: Cleve Moler on Mathematics and Computing
Cleve’s Corner: Cleve Moler on Mathematics and Computing The MATLAB Blog
The MATLAB Blog Guy on Simulink
Guy on Simulink MATLAB Community
MATLAB Community Artificial Intelligence
Artificial Intelligence Developer Zone
Developer Zone Stuart’s MATLAB Videos
Stuart’s MATLAB Videos Behind the Headlines
Behind the Headlines File Exchange Pick of the Week
File Exchange Pick of the Week Hans on IoT
Hans on IoT Student Lounge
Student Lounge MATLAB ユーザーコミュニティー
MATLAB ユーザーコミュニティー Startups, Accelerators, & Entrepreneurs
Startups, Accelerators, & Entrepreneurs Autonomous Systems
Autonomous Systems Quantitative Finance
Quantitative Finance MATLAB Graphics and App Building
MATLAB Graphics and App Building








Comments
To leave a comment, please click here to sign in to your MathWorks Account or create a new one.